Attack Surfaces: Networks and Infrastructure

Part 3 of the Attack Surfaces series
Modern networks and infrastructure present a complex and dynamic attack surface for organizations to defend. The prevalence of cloud hosting, shift to mobile and remote work, and growth of interconnected partner ecosystems have dramatically increased the number of potential entry points for threat actors to exploit. Monitoring, prioritizing, and protecting your organization’s external network attack surface is a complex problem with many facets. We break down the most common problems and solutions in this post.
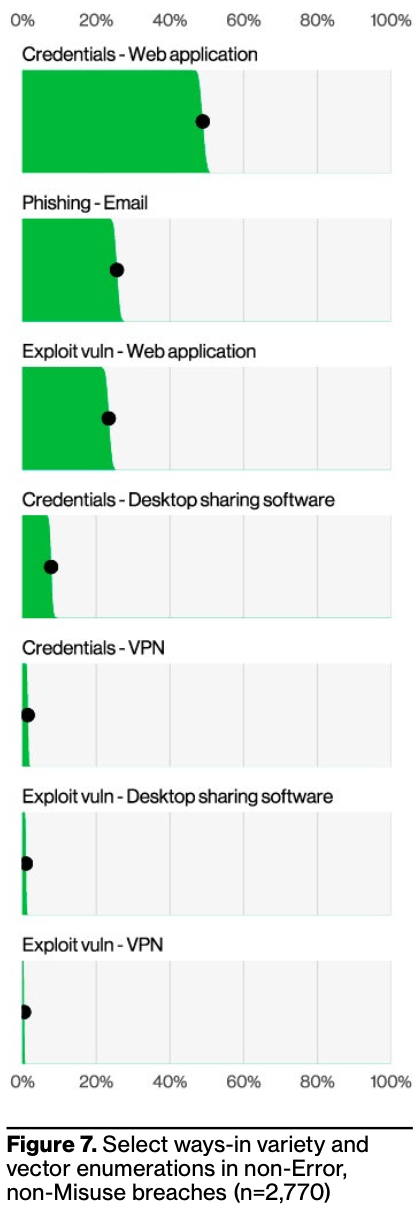
The 2024 Verizon DBIR has great stats on breach entry point. In 2023, exploitation of vulnerabilities as the critical path action initiating a breach increased 180% (this includes both applications + infrastructure vulnerabilities).
Organizations may become targets of opportunity and get caught in broad exploitation campaigns against a particular vulnerability. The CISA known exploited vulnerabilities (KEV) catalog lists vulnerabilities that have been or are being exploited in the wild. This list includes brand-new and, surprisingly, older vulnerabilities, such as CVE-2017-3506, which was discovered in 2017 but added to the KEV in June 2024. This vulnerability was patched and advisories issued in 2017, yet 7 years later, attackers are actively exploiting it.
Exposed Network Assets
Every internet-facing server, application, and device is a potential target for attackers continuously scanning for vulnerabilities to exploit. Exposed remote access services like RDP and VPN gateways are particularly attractive, as they can provide an immediate foothold for deeper network penetration. Inadequate network segmentation allows intruders to pivot and navigate towards higher-value systems once they gain an initial compromise. The 2024 DBIR specifically calls out desktop sharing software exposed directly to the internet as the initial vector in ~10% of breaches.
“Nothing is more permanent than a temporary solution”
Temporary or shadow IT assets can remain available long after their original purpose is fulfilled. While these assets used to (primarily) be physical assets in an office or datacenter and easier to visually spot, now they’re primarily virtual assets in a cloud environment, VMs, or containers which don’t have a physical footprint.
M&A introduces more complexity - acquisition targets bring their own legacy IT assets that may not be fully cataloged. Depending on how acquisitions are integrated, this may introduce risk to the acquiring entity.
To counter these risks, organizations must strive to know their own environments better than adversaries do. This requires a combination of continuous discovery to identify assets, business context to assess their criticality and inherent risk, and proactive monitoring for signs of compromise or suspicious activity. For crown jewels, assume a state of breach and implement robust detection and response capabilities.
Identity and Access Management
User credentials are one of the most sought-after resources for attackers (web application credentials were the first step in ~50% of 2024 breaches), as they immediately unlock access to sensitive data and systems (and may constitute a full breach by themselves). Managing identities across SaaS applications, cloud services, on-prem or custom applications, and devices is a highly complex task. Account sprawl, weak or reused passwords, and excessive privileges are common issues that introduce significant risk to an organization.
Sophisticated attackers are finding creative ways to circumvent multi-factor authentication controls, such as leveraging stolen session tokens or tricking users with advanced phishing techniques. Highly privileged accounts like service principals and API keys are also prime targets, as they can allow access to critical cloud infrastructure and resources.
Combating these threats requires a multi-layered approach spanning people, process, and technology. Baseline practices include enforcing strong authentication everywhere, applying least privilege access, and promptly de-provisioning unused accounts (automate where possible). More advanced organizations are exploring password-less authentication methods and just-in-time privilege elevation workflows to reduce risk.
Unmanaged/BYOD Assets
Unmanaged personal devices and Bring Your Own Device (BYOD) devices typically do not comply with corporate standards and may increase the risk of data leakage or individual device compromise. While these devices may be compromised in isolation, they should not be connected to any trusted segment of a corporate network. If a compromised device connects to a trusted corporate network, attackers can use it as a launchpad for reconnaissance and lateral movement.
To reduce the impact of a potential breach, endpoint privilege management and application controls can help enforce corporate policy across mobile and BYOD devices. The former involves eliminating local admin rights wherever possible to contain an attacker’s ability to steal credentials or disable security tools. The latter entails whitelisting authorized software and restricting execution of anything not explicitly allowed to help prevent malware from running.
IoT and OT Security
The billions of deployed IoT and operational technology (OT) devices present unique security challenges due to their constrained resources, long lifespans, and often insecure-by-design nature. Many of these devices run outdated operating systems or have hardcoded passwords that can’t be changed, making them easy scriptable targets for attackers (especially after vulnerabilities are discovered and published).
Gaining visibility into the full extent of an organization’s IoT/OT assets requires taking an inventory of all connected devices, identifying those which are exposed to the Internet, and assessing baseline configurations. Because many of these devices cannot be modified and/or have limited configuration options, controlling their network access can be the most practical mitigation. Network access controls can be applied to restrict IoT/OT systems to communicating only with authorized services and to isolate them from the rest of the network.
Cloud Security
While cloud servers can eliminate entire classes of traditional server vulnerabilities, they introduce new types of vulnerabilities that are generally less well-understood by the engineering community. Misconfigurations like exposed storage buckets or excessive IAM permissions are common entry points for attackers and have led to many notable breaches over the last decade+. The ephemeral nature of many cloud workloads makes it difficult to maintain an accurate inventory and assess the security posture at any given point in time and while cloud security tooling is catching up, this was a difficult problem until more recently.
Third-party risk is also heightened in cloud (including SaaS) environments, as organizations rely on a web of external service providers and must navigate shared responsibility models. An attacker who compromises a cloud provider could potentially impact all of their customers, turning a single exploit into a massive breach. More recently, we’ve also seen the significant risk of supply chain attacks targeting open source components used in cloud workloads and applications.
To manage cloud security risks, consider infrastructure-as-code and DevSecOps principles, cloud security posture management (CSPM) tooling, network segmentation (including micro-segmentation), and granular access control across cloud environments.
Final Thoughts
Today’s adversaries are more sophisticated and relentless than ever, and the attack surface will only continue to expand as technology evolves. To stay ahead, organizations must think like an attacker and continuously probe their own defenses. Penetration testing and red teaming help validate controls and identify weaknesses before criminals exploit them.
Ultimately, there is no impenetrable perimeter in the modern extended enterprise. Defenders must assume compromise and focus on strengthening their ability to rapidly detect, isolate, and recover from incidents. By gaining deeper visibility across their environment, armed with right set of insight and analytics, organizations can adapt and withstand constant attacker probing and exploitation attempts.
