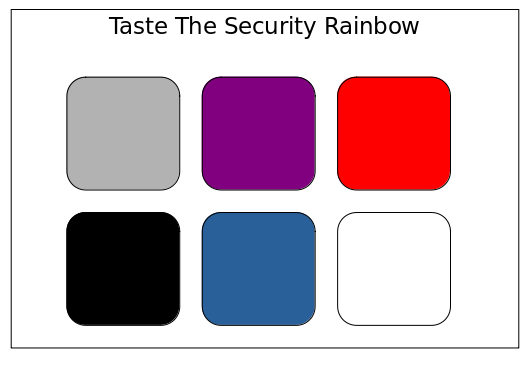
Security Assessment Color Palette
There are many different types of security assessment methodologies identified by cute color associations. Here are simple descriptions of the most popular to help you choose which approach is right for you. Your opinion on these descriptions may differ from mine, and if so, I’d love to hear from you.
Whitebox Security Assessment: a comprehensive security assessment where assesors have unfettered access to inside information, such as source code.
A whitebox assessment requires complete transparency between the creators of a system and the people performing the security assessment. Whitebox often implies a comprehensive review of source code and configuration files. You probably want a whitebox assessment if:
- You have a business requirement to thoroughly investigate all the security properties of a system or application
- You have the time and money to perform such a thorough assessment, and are prepared to act on the results
Blackbox Security Assessment: the polar opposite of a whitebox assessment, blackbox means that assessors have zero access to private information about the system.
A blackbox assessment offers zero insider knowledge or collaboration to the people performing the assessment, ultimately slowing down the assessment and making it harder to identify vulnerabilities. You probably want a blackbox assessment if:
- You don’t need to identify and remediate the highest impact security issues as quickly and efficiently as possible
- You need to check a box that says you had a penetration test and don’t want to spend any more time thinking about it
Greybox Security Assessment: an assessment performed similarly to a blackbox assessment, however some inside information, such as source code, is made available to the assessors.
A greybox assessment allows for faster and more accurate identification of high impact vulnerabilities when compared to a blackbox assessment, but with less expense and effort when compared to a whitebox approach. You probably want a greybox assessment if:
- You have a fixed budget and timeframe to perform your assessment
- You need to identify and remediate the highest impact security issues as quickly and efficiently as possible
Red-Team: a zero knowledge adversarial simulation designed to compromise an organization and demonstrate unauthorized access to specific targets
Red-Team engagements are typically performed to test the efficacy of an existing security program. These engagements typically have specific targets of interest inside of an organization, but allow assessors to use a wide variety of adversarial techniques ranging from social engineering to application layer attacks in order to achieve their objectives. These engagements often require more time and budget than typical blackbox and greybox assessments. You probably want a Red-Team if:
- You have already invested in a security strategy and have implemented controls and best practices throughout the organization
- You think your organization is “good” at security and want to assess your ability to detect, respond, and control a targeted attack and breach
- You know that your organization is not adequately prepared for a real attack and need fire-works to show senior management and get them onboard to invest
Purple-Team: similar to a red-team, but performed in a collaborative manner with defensive security teams.
Red-Teams are typically performed without any warning or involvement from teams inside the target organization. As a result, much of the value to organization is created after the engagement is complete, through a written report, debriefing of the vulnerabilities discovered, and remediation of issues. Purple-Team assessments aim to increase the time-to-value to the organization through collaboration between attack teams and defense teams. This approach allows defensive teams to tune process and tools in real time to better detect tactics employed by the attack teams. You probably want a purple team if:
- You already have defensive teams and tactics, techniques, and procedures that can be improved upon
- You know your organization needs help and want to accelerate the rate at which you mature security operations and procedures.
Blue-Team: a collaborative engineering exercise designed to produce a purposefully secure system, application, or product.
Most security assessments happen out-of-band or after-the-fact relative to building and deploying new technologies. In a Blue-Team engagement, security engineers work hand-in-hand with architects and engineers to use threat modeling, secure coding concepts, and other proactive security tools and procedures address security earlier in the lifecycle of a project. Blue-Teams reduce the risk of show-stopping security issues delaying your launch and the risk of a post-launch breach. You probably want a Blue-Team if:
- You are building something new that is of high importance to your organization
- You want to ensure the new system is released to production on time and without excess risk to the organization
- You want to reduce the risk of show-stopping security vulnerabilities jeopardizing your launch or a business deal
